TimeTac offers the opportunity to configure Single Sign-On (SSO) as authentication method for your account. Single Sign-On allows your employees to sign in using their corporate credentials instead of their TimeTac credentials.
Advantages of SSO
- Leverage existing company’s authentication
- Better security when employees use company’s established password
policies rather than their individual accounts - Seamless user experience due to the ability for employees to log in just one time with one set of credentials to get access to all corporate apps
Supported SSO Protocols
Currently, TimeTac supports any identity provider which supports SAML 2.0 protocol. We offer tutorials and technical support for the following identity providers: Microsoft Azure and Google GSuite.
If you are interested in configuring SSO with an identity provider where we do not provide technical documentation yet, you can contact us via email (support@timetac.com) for further information.
Prerequisites
- User with full employee access
- Identity Provider (IdP) administrative privileges
- E-mail addresses of users are managed in TimeTac
- Please note that e-mail addresses are the only TimeTac identifier which can be used for user identification at this moment in time
- If you require a different identifier, please contact us at support@timetac.com
Configuring Single Sign-On
To configure SSO for your TimeTac account, take the following steps:
Connection to your Identity Provider
To enable SSO for your TimeTac account, you have to create a TimeTac application on your identity provider side. For the SAML configuration you need to set the Identifier field (Entity ID) and the Reply URL (ACS URL) and define a User Identifier:
- Identifier field: The identifier field is a predefined link that points out to a part of the TimeTac system which handles SAML communication. Please use https://go.timetac.com/{{accountName}}/modules/saml/consume.php. The {{accountName}} is a variable and should be replaced with your TimeTac company account name.
- Reply URL field:
Please use https://go.timetac.com/{{accountName}}/modules/saml/consume.php. The {{accountName}} is a variable and should be replaced with your TimeTac company account name. - Unique User Identifier: TimeTac uses the value of the NameID to identify the employee and expects it to be the email address.
TimeTac provides detailed technical documentation on how to set up SSO with the following identity providers:
- Azure AD: https://support.timetac.com/en/sso-en/microsoft-azure/
- Google Workspace: https://support.timetac.com/en/sso-en/setting-up-sso-with-google-workspace/
Getting started with SSO in TimeTac
To get started with your SSO configuration, take the following steps:
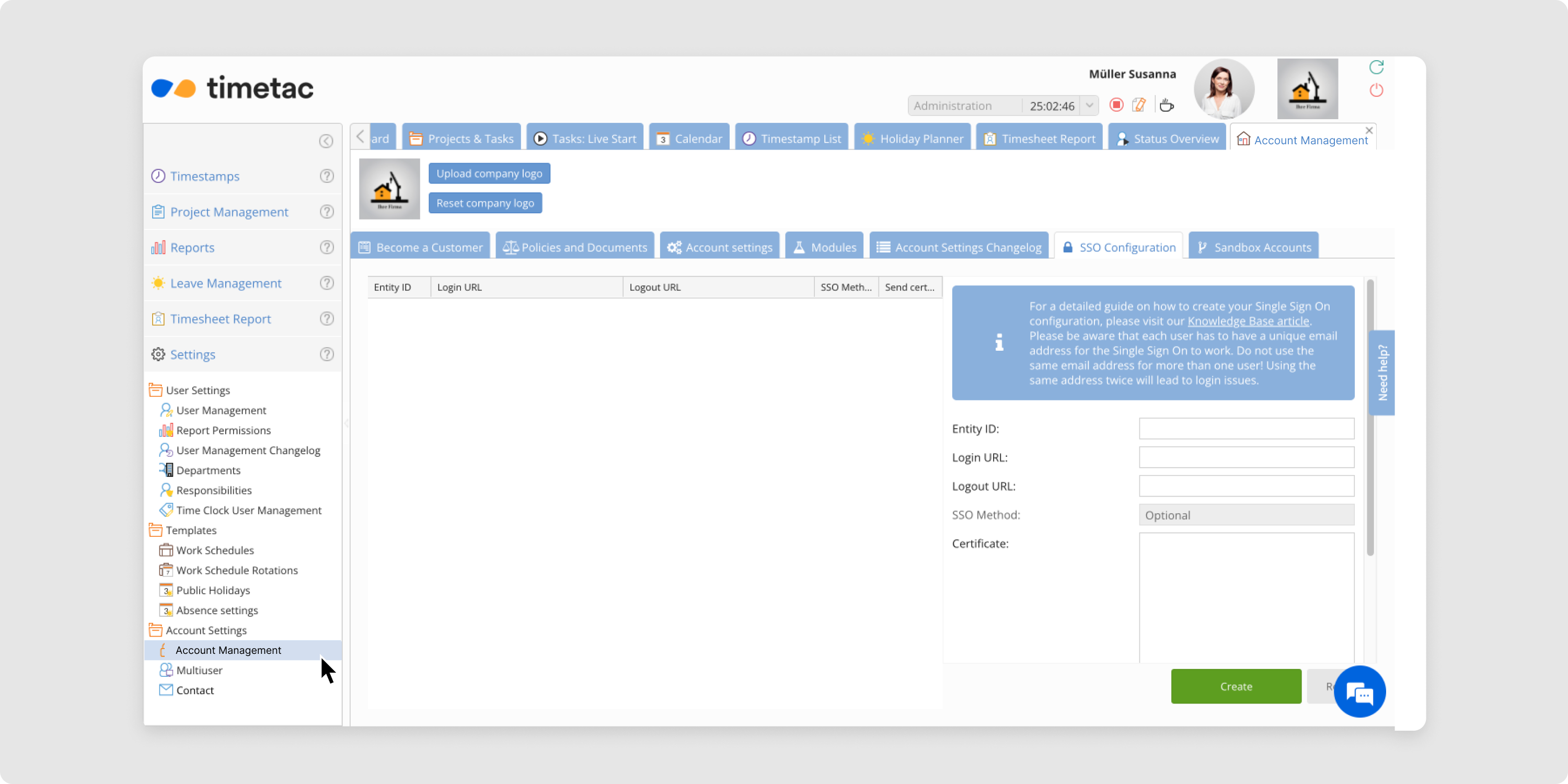
- Login in to your TimeTac account with an administrator user.
- Click on the menu Settings and then select Account Management.
- Go to the section SSO Configuration and start configuring TimeTac as SSO Service Provider by filling in the Service Provider Details provided by your Identity Provider. Therefore, enter the data in the following fields:
- Entity ID: globally unique name for an Identity Provider
- Login URL: identity provider’s endpoint (URL) that is responsible for handling a SAML transaction
- Logout URL: redirect URL where the user will be redirected to after logging out of the service provider
- Signing Certificate: required to encrypt and decrypt a SAML assertion. Open the certificate that you have downloaded from your Identity Provider with a text editor and copy/paste it into the certificate field.
- After you have completed your configuration, enable SSO by clicking on the Create button.
- Test the SSO login by logging out of your account and try to log in again. SSO is configured to be optional, this means you will be able to choose if you would like to log in with SSO or your TimeTac credentials. Instead of filling in your TimeTac credentials, click on the button Login with SSO. You will get redirected to your identity provider’s login screen for authentication. When you are successfully authenticated, you will be redirected to your TimeTac account.
Verifying your SSO Setup
Verify that you have correctly integrated with your Identity Provider:
- A TimeTac application is configured in your Identity Provider
- Your employees are granted access to the TimeTac application configured in your IdP
- The SAML Subject NameID value that is sent in the SAML response is configured to be the email address of the employee
- The email address of your employees is maintained and unique in TimeTac, as it will be used as a matching key to identify a user.
Make the SSO login required
Once SSO has been successfully set up and tested, it is possible to define SSO as a mandatory login, i.e. your employees can then log in exclusively via SSO. A login with the TimeTac credentials is no longer possible.
To configure SSO as a mandatory login method, make the following setting:
- Click on the menu Settings and then select Account Management.
- In the SSO Configuration menu option you find the details of your already existing SSO configuration.
- Change the SSO Method from optional to required.
- Click on update.
Before changing this setting, please ensure that the SSO configuration works, otherwise nobody will be able to log in anymore and you will need to request assistance from our Support team.
Deactivate an existing SSO configuration
In case your existing SSO configuration is not working or you would like to switch to a different Identity Provider take the following steps to deactivate an existing SSO configuration:
- Click on the menu Settings and then select Account Management.
- In the SSO Configuration menu option, you find the details of your already existing SSO configuration.
- Click on the Deactivate button to remove the existing SSO configuration.
If you need any help configuring SSO for your TimeTac company account, we are looking forward to your request via email: support@timetac.com.